Tristan Stiller
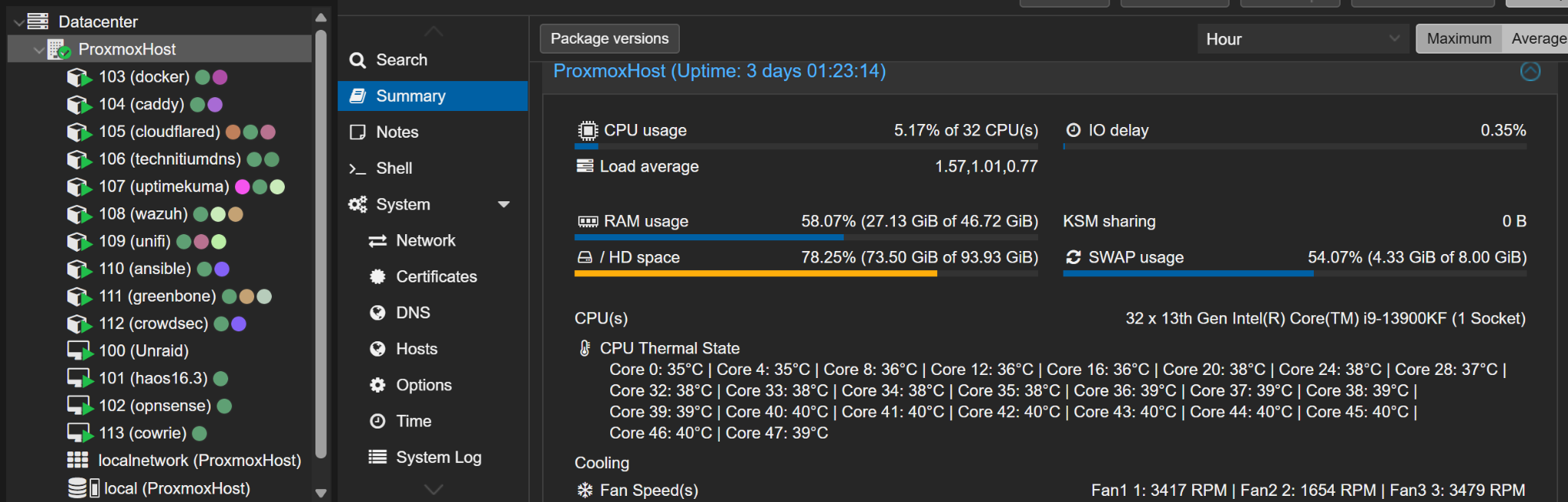
ECE student at Vanderbilt University building production-grade security, networking, and local AI automation systems. I operate a segmented Proxmox homelab with GPU-hosted specialist models, a deterministic local voice pipeline, and a public AI-enriched threat intelligence feed publishing STIX 2.1/TAXII 2.1 indicators from live SSH honeypot attacks.
Electrical and Computer Engineering at Vanderbilt University, Class of 2027. I design, deploy, and operate production security infrastructure that processes live internet threats around the clock.
Seeking internships in security engineering, infrastructure, and networking. Currently studying for CompTIA Network+, CCNA, and Security+.
Lab Overview
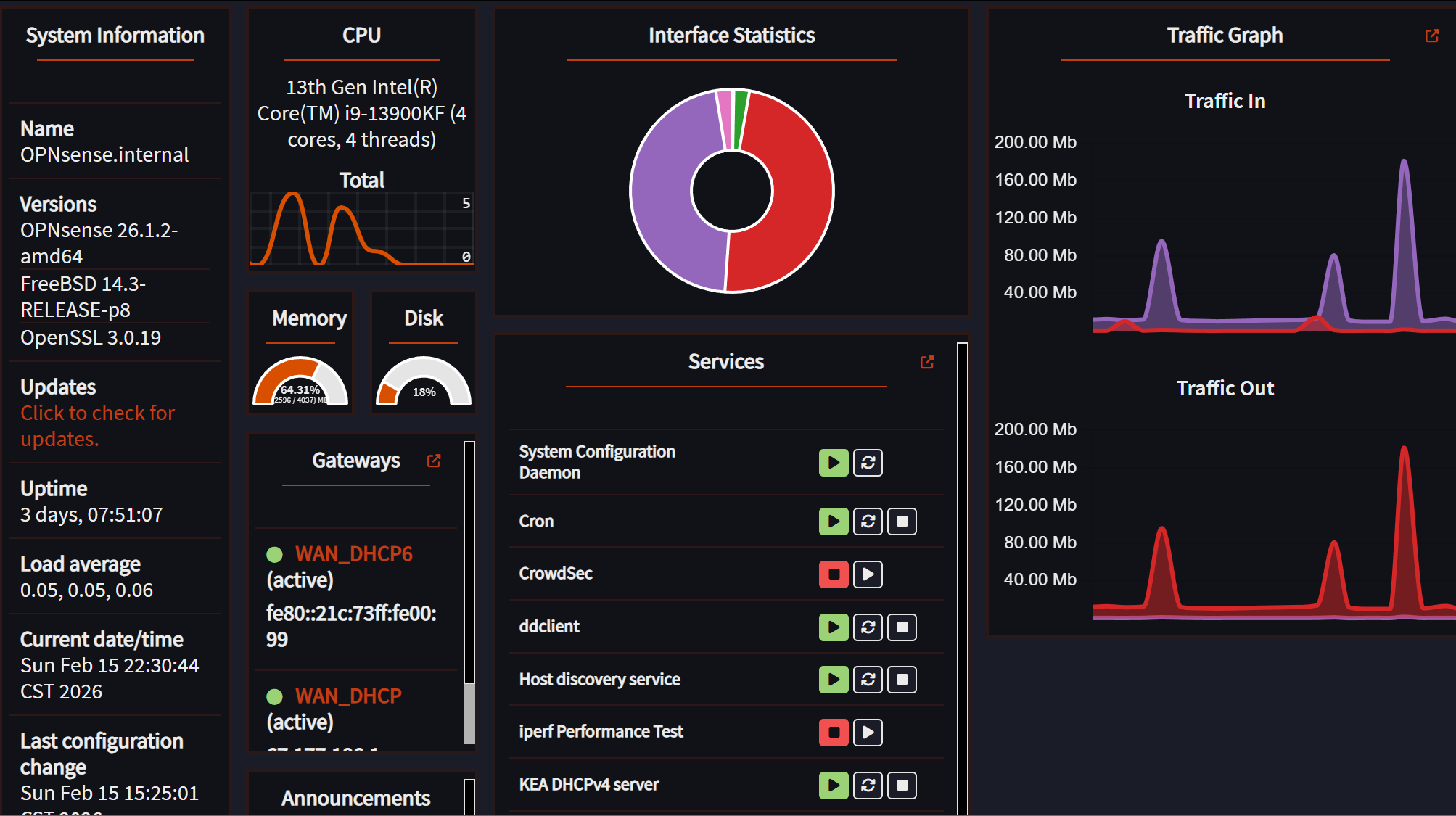
A two-node Proxmox lab running core security, network, storage, and local AI services with SR-IOV networking, native IPv6, multi-VLAN segmentation, GPU specialist models, and a full security stack - processing live internet attacks 24/7.
AT&T Fiber · IPv4 passthrough + native IPv6 PD
Suricata IPS · WireGuard VPN · NAT · DNS Intercept
Default-deny · All DNS → Technitium
192.168.1.0/24
2601:…:12aa::/64
Docker (~40ct) · Technitium
CrowdSec · Authentik SSO
Prometheus · Grafana
192.168.30.0/24
Native IPv6 /64
Zigbee · Z-Wave
Alexa (Lambda)
192.168.40.0/24
Native IPv6 /64
Client isolation
No inter-VLAN routing
192.168.99.0/24
Native IPv6 /64
WAN:22 → :2222
AI deception (4B Q8)
Outbound-only · Zero inbound ports
Forward auth · 23 services
*.101904.xyz · acme.sh
Custom Engineering
The difference between installing software and building systems. These are components I designed, wrote, and debugged from scratch.
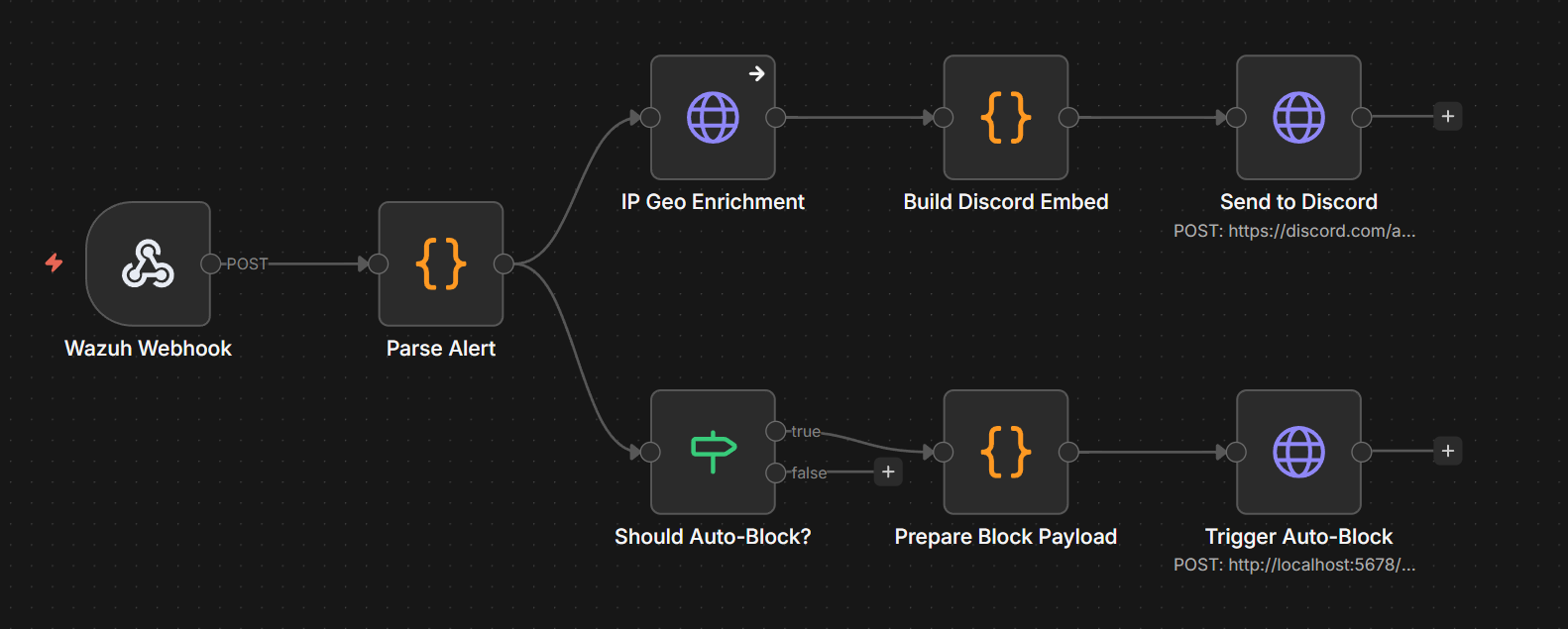
SOAR Pipeline (Wazuh → N8N → CrowdSec → OPNsense)
Custom alert enrichment workflow: Wazuh fires on level 10+ events → N8N enriches with GeoIP → CrowdSec bans for 24h → OPNsense pf table blocks at the firewall. Dual-blocking with automatic expiry sync.
AI-Augmented Honeypot
GPU-hosted Cowrie specialist model generates realistic shell responses for unknown commands. Attackers see fake DB credentials, bash history, and system info instead of "command not found," keeping sessions alive long enough to capture better TTPs.
TinyHA Deterministic Voice Router
Replaced the old HA 2B specialist path with a tiny deterministic CNN router that renders structured Home Assistant actions, blocks ambiguous aliases, logs live corrections, and only escalates edge cases to a guarded 27B local fallback.
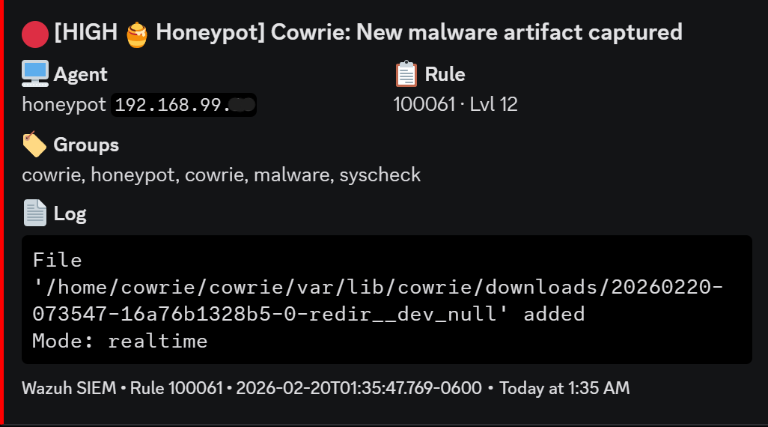
26 Custom Wazuh Detection Rules
Hand-written rules for Cowrie (100050-100061), Authentik SSO (100100-100108), and Caddy access logs (100200-100204). Static field mapping, JSON decoder integration, evaluation ordering.
Daily Security Digest
Automated 8AM briefing via N8N cron: queries Wazuh API for alert counts, top attacker IPs, firewall state table, and CrowdSec ban summary. Posts to Discord with severity-colored embeds.
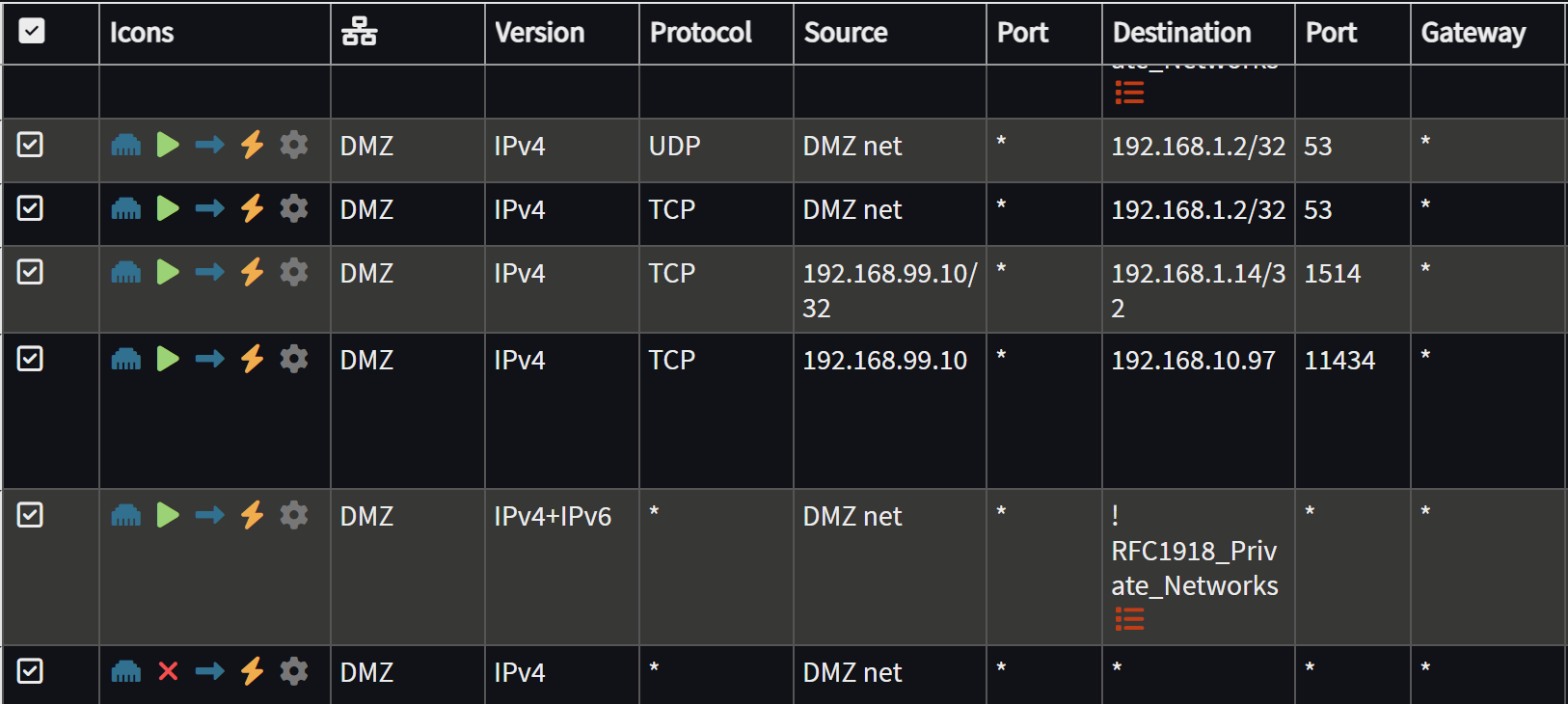
IPv6 DNS Enforcement + Transport Hardening
Native AT&T IPv6 delegated across LAN, workstation, IoT, guest, and DMZ networks. OPNsense pf rules mirror the IPv4 default-deny posture and enforce Technitium DNS. DoT (853 TCP), DoQ (8853 UDP), and DoH to known providers are blocked except explicit allowlisted resolvers.
Local AI Voice Assistant (ha-voice)
Fully local, offline voice pipeline across ESPHome ESP32-S3 mic satellites: M18 GPU Parakeet STT, CT103 TinyHA deterministic intent routing, direct Home Assistant API calls, silent/chime response path, and Qwen 27B fallback for rare ambiguous commands. All inference stays on-premises.
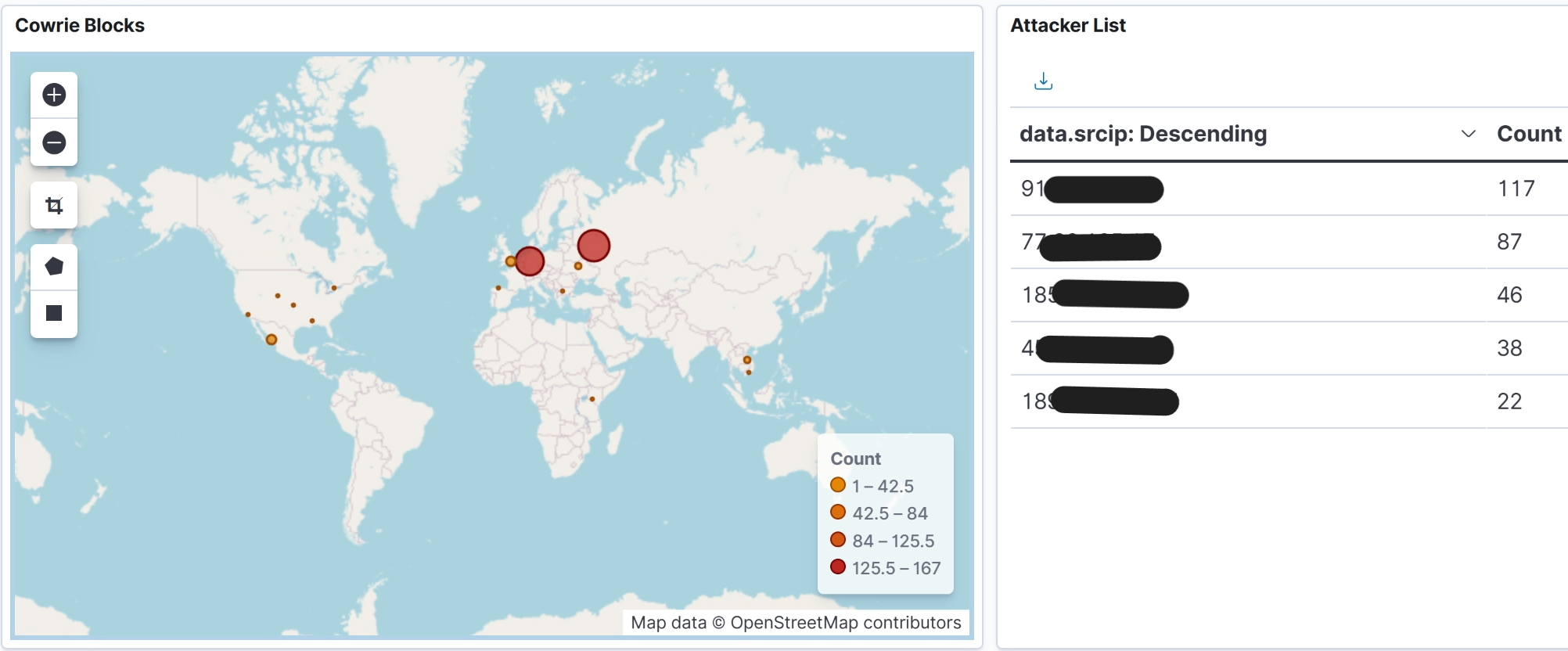
Public Threat Intel Feed (STIX 2.1 + TAXII 2.1)
AI-enriched threat intelligence API (v1.5.1) publishing 39K+ indicators from 154K+ live honeypot sessions. Attack data is classified by a local specialist model with rule guardrails, mapped to MITRE ATT&CK, and served as JSON, CSV, streaming STIX 2.1, or TAXII 2.1 with cursor pagination. No API key required.
Docker Crash Watcher
Custom systemd service monitoring Docker container exits. Posts Discord embeds on non-zero exit codes with 10-minute per-container cooldown to prevent alert storms. Ignores graceful stops (SIGTERM).
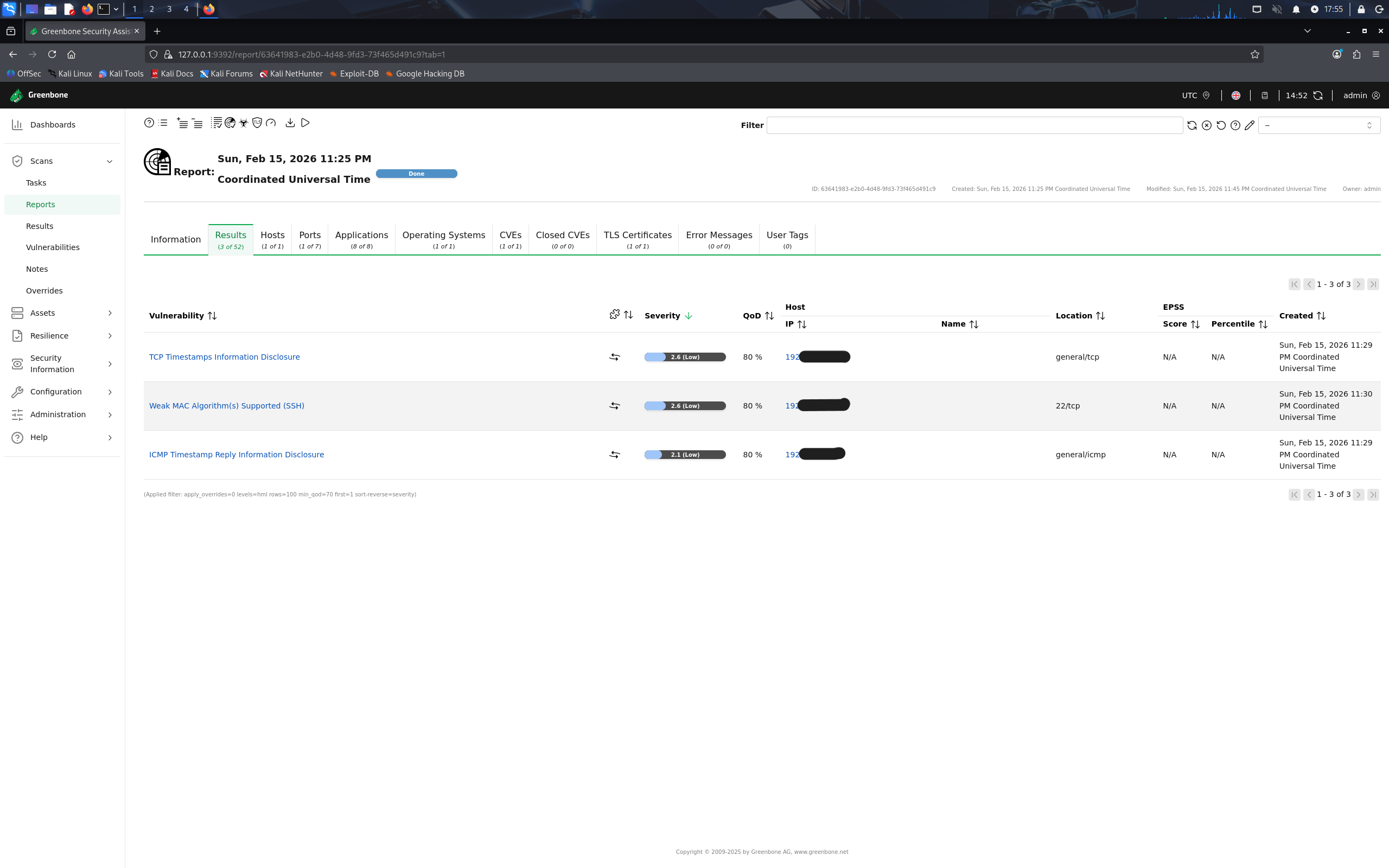
Automated Vulnerability Scanning Pipeline
Scheduled Greenbone/OpenVAS scans run MWF at 3AM via cron. Auto-starts the CT, runs full network scans across all VLANs, and shuts down after completion to conserve resources. Results feed into Wazuh for correlation with real-time alerts.
Design Philosophy
Local AI Automation
On-premises specialist models for smart-home control, honeypot deception, threat classification, documentation search, and guarded fallback reasoning. The design favors deterministic fast paths first, with larger LLMs reserved for ambiguous cases.
Wake + microphone
Parakeet / Wyoming
Deterministic action JSON
Direct LAN call
Guarded fallback
TinyHA Voice Control Path
Home Assistant voice commands are routed through a tiny deterministic model instead of a general-purpose chat model. The fast path produces validated JSON/action calls; uncertain requests fall back to the larger local model instead of guessing.
- Router: live TinyHA service reports
tinyha-cnn-small-v4with 57 current HA entities and 269 TinyHA entity aliases indexed - Latency-first placement: TinyHA runs on the Docker LXC beside the HA API path; STT and chime run on the M18 AI node
- Safety controls: confidence thresholds, ambiguous-alias blocking, deterministic JSON rendering, compound-command splitting, and live transcript/correction logging
- Fallback: Qwen 27B remains available for rare commands that need broader language reasoning
GPU Specialist Model Stack
Specialist services are served locally using OpenAI-compatible endpoints so automation code can swap models without changing callers.
- Cowrie: Qwen 3.5 4B Q8 specialist for honeypot shell-response generation
- Threat intel: Qwen 3.5 4B Q6_K_P specialist for attack classification, MITRE mapping, and review-aware enrichment
- Fallback assistant: Qwen 27B GGUF on the RTX 5080 workstation, exposed through a LAN proxy for guarded local reasoning
- Knowledge base: Open WebUI + RAG Drop ingest Wiki.js/homelab docs so the local assistant can answer operational questions from current lab documentation
Deterministic HA JSON Renderer
Converts classified utterances into stable Home Assistant service calls rather than free-form prose. This keeps the common path fast, auditable, and safe to execute.
Live Data Collection Loop
Voice transcripts, correction logs, entity aliases, and threat-review exports feed future dataset rebuilds. The training workflow can improve models without depending on one-off manual prompt tuning.
Guarded 27B Fallback
The largest local model is reserved for complex or ambiguous requests, while deterministic specialists handle routine control and classification. This preserves latency without removing a reasoning escape hatch.
Operations-Aware RAG
Wiki.js pages and upgrade runbooks are synced into a local RAG workspace for documentation-grounded troubleshooting, including the staged BlueField networking upgrade pack.
Detection → Enrichment → Response Pipeline
A fully automated SOAR pipeline that detects attacks on the honeypot, enriches alerts with threat intelligence, and blocks malicious IPs at the firewall - all within 30 seconds, with no human intervention required.
Public Internet
WAN:22 → DMZ
VLAN 99 (DMZ) + AI
JSON Log Ingestion
Rule Matching
Enrichment + Routing
24h Ban Decision
WAN Block Rule
STIX 2.1 + MITRE
Stage 1: Cowrie SSH Honeypot + AI Deception
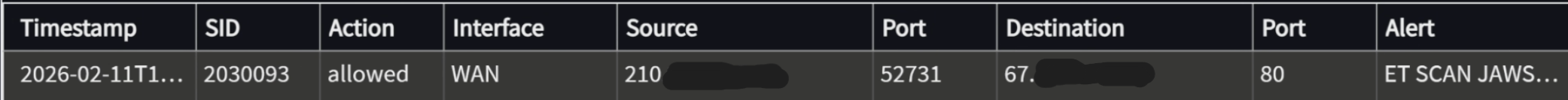
A medium-interaction SSH honeypot in an isolated DMZ (VLAN 99) with public SSH (WAN port 22) redirected via OPNsense NAT. Captures credential stuffing, shell commands, and malware drops from real attackers.
- Isolated in DMZ VLAN 99 - no lateral movement to production networks
- AuthRandom authentication: randomly accepts credentials after 1-3 attempts to maximize session depth
- Fake SSH banner:
SSH-2.0-OpenSSH_6.0p1 Debian-4+deb7u2- looks like a vulnerable Debian 7 server - AI-augmented responses - local llama.cpp Cowrie specialist generates realistic Ubuntu server terminal output, with fake DB credentials, bash history, and crontabs to maximize attacker dwell time
- Malware downloads captured to disk, monitored by Wazuh FIM with VirusTotal integration
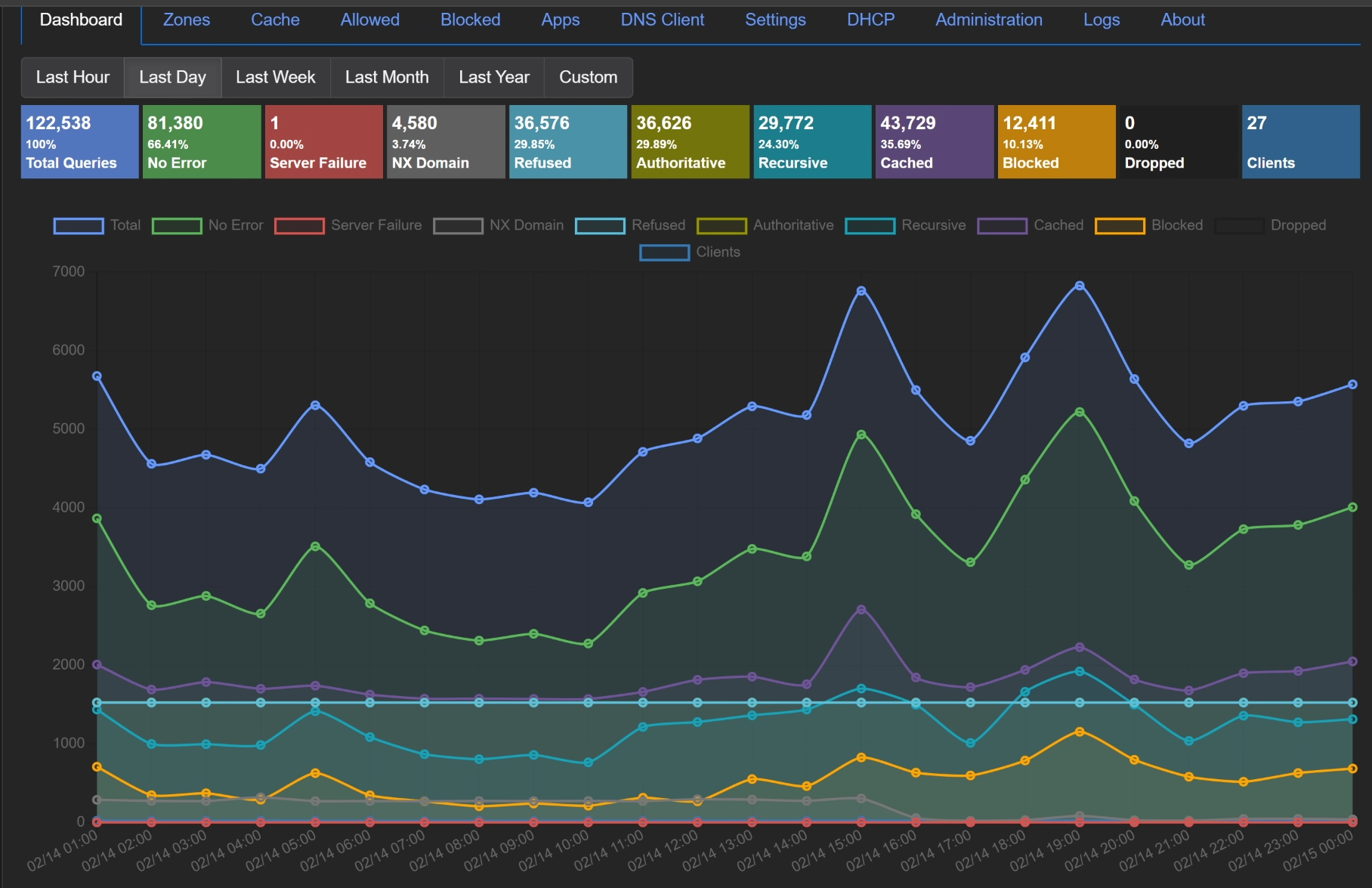
Stage 2: Wazuh SIEM - Detection Engineering
26 custom rules across 3 rule files process JSON logs from Cowrie, Authentik SSO, and Caddy reverse proxy. The native JSON decoder extracts fields; rules use static field tags and ordered evaluation for precise matching.
- Cowrie rules (100050-100061): connection, login success/fail, commands, file download/upload, brute-force frequency, dangerous commands (wget/curl/reverse shells), cryptominer detection, persistence attempts
- Authentik rules (100100-100108): auth failures, brute-force (5 in 60s), flow execution, admin API mutations, 401/403 responses, worker task failures
- Caddy rules (100200-100204): 4xx/5xx errors, 403 blocks (CrowdSec), web scanning detection (10+ 4xx in 30s)
- Level 10+ alerts automatically trigger the N8N SOAR pipeline
- Level 12 FIM events (malware artifacts) trigger VirusTotal hash lookup
Stage 3: N8N SOAR - Enrichment & Auto-Block
Three custom N8N workflows process Wazuh alerts in real time, enrich them with threat intelligence, and execute automated response actions.
- Alert Enrichment + Auto-Block: receives webhook from Wazuh integratord → enriches with ipwho.is GeoIP → categorizes by severity/type → posts color-coded Discord embed → triggers CrowdSec ban
- CrowdSec Auto-Block: dual-blocks attackers - CrowdSec 24h ban + OPNsense n8n_blocklist pf table (WAN inbound block rule)
- Daily Security Digest: 8AM cron queries Wazuh API for overnight alert summary, top attacking IPs, pf state table stats → Discord briefing
- Blocklist sync cron every 2h: reconciles CrowdSec ban list with OPNsense pf tables, removes expired IPs
Stage 4: Public Threat Intel Feed
Attack data from the SOAR pipeline is published as a free, public threat intelligence API. Sessions are classified by a local specialist model with rule guardrails and mapped to MITRE ATT&CK techniques.
- 154K+ sessions indexed, 39K+ indicators, 29 captured malware samples from live attacks
- Streaming STIX 2.1 - async generator pages DB in batches; no OOM risk. TLP:CLEAR marking, kill chain phases, MITRE ATT&CK relationships
- TAXII 2.1 endpoint - spec-compliant Envelope format, cursor pagination,
added_afterincremental sync,X-TAXII-Date-Added-Lastheader - AI classification via local OpenAI-compatible specialist endpoints with deterministic rule guardrails and review-status metadata
- MITRE ATT&CK: T1110 brute force, T1110.004 credential stuffing, malware deployment, cryptominer installation
- Rate limiting, pagination, filtering by threat level / attack type / time range. Current public API: v1.5.1
- Source: github.com/Tristan1019-user/honeypot-threat-intel
Why I Built It This Way
→ Why block at the firewall, not the host?
CrowdSec and OPNsense pf tables enforce bans at the network perimeter. Host-level blocking (iptables, fail2ban) only protects one service - a firewall rule blocks the attacker from reaching anything, including services that don't have their own IPS.
→ Why dual-block (CrowdSec + OPNsense pf)?
CrowdSec bans expire automatically (24h TTL). OPNsense alias config persists across reboots but pf tables don't auto-populate from aliases. The 2-hour sync cron reconciles both - live pf table for immediate blocking, alias config for reboot persistence.
→ Why an AI honeypot?
Standard Cowrie returns "command not found" for ~80% of attacker commands, which is a dead giveaway. The local specialist model generates plausible Ubuntu server output (fake DB credentials, bash history, crontabs), keeping attackers engaged longer and capturing more TTPs without API costs or data exfiltration.
→ Why custom Wazuh rules instead of default rulesets?
Default Wazuh rules don't understand Cowrie's JSON schema or Authentik's structured logs. Custom rules with decoded_as: json and field-level matching extract attacker IPs, usernames, and commands directly from the JSON, enabling precise alerting and correlation that generic syslog rules can't achieve.
Security Architecture
A layered security stack with 7 Wazuh agents across 4 VLANs, automated threat response, and continuous vulnerability assessment.
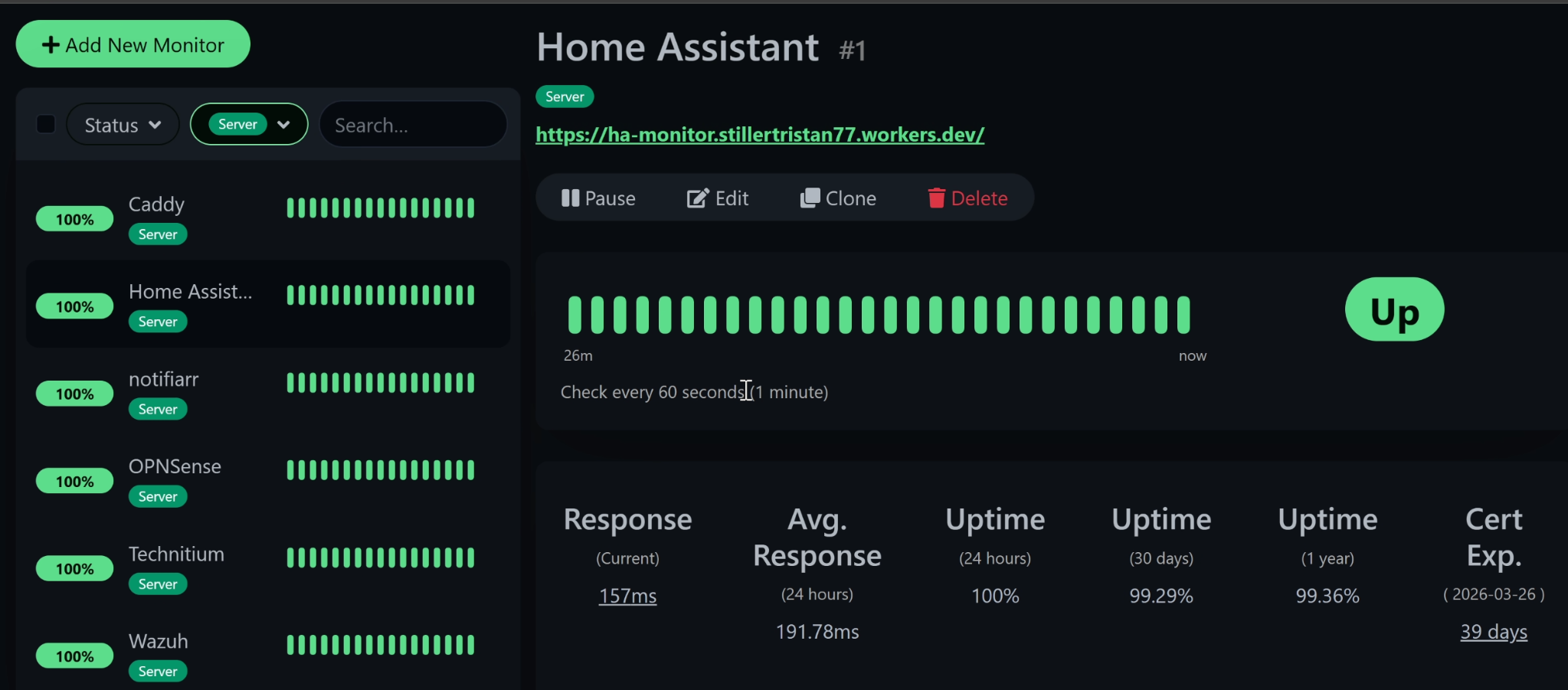
OPNsense Firewall
Stateful firewall with Suricata IPS (ET-Pro rules, netmap mode on WAN), multi-VLAN routing, NAT, and DNS interception. Acts as the network's root of trust.
Wazuh SIEM
Centralized SIEM with 7 active agents on Proxmox, Docker, Caddy, OPNsense, Cowrie, Zenbook, and workstation. 26 custom rules, FIM, and VirusTotal integration.
Cowrie Honeypot + AI
SSH honeypot in DMZ VLAN 99 with AI-generated responses via local llama.cpp LLM. Captures credentials, commands, and malware from real attackers daily.
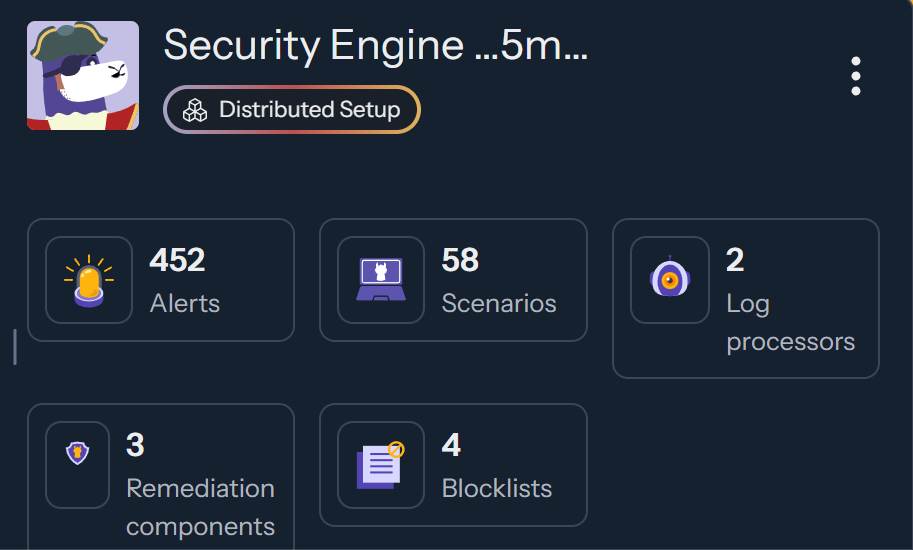
CrowdSec IPS
Collaborative behavioral IPS. Receives ban decisions from N8N SOAR pipeline and enforces at the OPNsense firewall. 24h TTL with automatic expiry.
Greenbone Vulnerability Scanner
OpenVAS in a Kali LXC with RAM-constrained sequential scanning (max_hosts=1, max_checks=3). Automated 3x/week via cron - Monday (core infra), Wednesday (Docker), Friday (all LXCs). Results posted to Discord. CT auto-starts for scan, stops after.
Authentik SSO + Cloudflare Access
Domain-level forward auth across 23 services. Cloudflare Access gates external apps with Google MFA; Authentik provides OIDC SSO for all internal services via Caddy.
Access Control Stack
Multi-layer identity and access management with zero-trust principles. No inbound firewall ports - all external access via Cloudflare Tunnels.
- Cloudflare Access enforces Google account allowlisting before any app is reachable
- Authentik SSO provides domain-level forward auth for 23 internal services via Caddy reverse proxy
- OIDC/SAML with embedded outpost - outpost passthrough handles OAuth callbacks without redirect loops
- Vaultwarden for credential management (self-hosted Bitwarden with its own 2FA)
- SSO exclusions for services with native auth: Jellyfin (API key), Vaultwarden (own 2FA), Home Assistant
MWF 3AM CST
Greenbone/OpenVAS
Mon: Core · Wed: Docker
Fri: All LXCs
CVSS severity scoring
Findings embed
RAM reclaimed
Advanced Networking
Enterprise-grade networking with SR-IOV, multi-VLAN segmentation, IPv6 dual-stack, hardened DNS, and zero-exposure external access.
SR-IOV - Mellanox ConnectX-5
16 Virtual Functions on a ConnectX-5 dual-port 25GbE NIC, each assigned directly to VMs and containers for near-native network I/O with hardware-level traffic isolation.
- Each VM/LXC gets a dedicated SR-IOV VF - bypasses the host network stack entirely
- VF-level VLAN tagging enforced at the PF for DMZ isolation (VLAN 99)
- Trust and spoofcheck configured per-VF via Proxmox hookscripts for persistence across reboots
- PCIe passthrough for OPNsense (full NIC control) and Unraid (SATA controller)
IPv6 Dual-Stack + DNS Enforcement
Full native IPv6 deployment using AT&T delegated prefixes across internal networks, with DNS enforcement and default-deny firewalling that mirrors the IPv4 posture.
- LAN, workstation, IoT, guest, and DMZ networks receive native delegated /64s instead of private-only ULA addressing
- radvd advertises the delegated prefixes and DNS options consistently after OPNsense config regeneration
- OPNsense pf
rdr inet6intercepts IPv6 port 53 traffic on every VLAN → Technitium DNS - DoT (853 TCP), DoQ (8853 UDP) blocked on all LAN interfaces. DoH blocked to 33 known providers via firewall alias; Cloudflare and Quad9 explicitly permitted
- Persistent patch script repairs radvd.conf and kea-dhcp6.conf after every OPNsense config regeneration (runs every 10 min via cron)
- avahi-daemon on OPNsense bridges mDNS across LAN, VLAN 30, VLAN 40, and workstation for AirPlay, HomeKit, and Spotify Connect discovery
4 VLAN Segmentation
Production (default), IoT (VLAN 30), Guest (VLAN 40), DMZ (VLAN 99). Inter-VLAN routing only through OPNsense with explicit per-service allow rules. Default-deny between all zones.
Technitium DNS - Hardened (IPv4 + IPv6)
Self-hosted recursive DNS with Cloudflare and Quad9 DoH upstreams. OPNsense intercepts ALL DNS (port 53) on both IPv4 and IPv6 via pf rdr rules - clients cannot bypass it. DoT (853), DoQ (8853), and DoH to 33 known providers explicitly blocked. mDNS reflected across VLANs via avahi for AirPlay and HomeKit discovery.
Cloudflare Tunnels + Caddy
Outbound-only tunnels replace port forwarding. Caddy reverse proxy with ZeroSSL wildcard cert (*.101904.xyz) routes to all internal services. Zero inbound firewall exposure.
WireGuard VPN (OPNsense)
Site-to-site and remote-access VPN terminated directly on OPNsense. Firewall rules enforce the same VLAN segmentation and default-deny posture for VPN clients as local traffic - no split-tunnel bypass.
UniFi Enterprise Wireless
Managed access points with SSID-to-VLAN mapping, client isolation, and centralized controller for configuration and monitoring.

Automation, IaC & Monitoring
Infrastructure-as-code, workflow orchestration, automated monitoring, and Git-backed configuration management.
Ansible - Infrastructure as Code
Configuration management playbooks for LXC containers and host-level settings. Package installation, service configuration, and security baselines - all version-controlled.
N8N - SOAR Workflows
3 active SOAR workflows: Alert Enrichment + Auto-Block, CrowdSec Dual-Block, and Daily Security Digest. Webhook-triggered by Wazuh integratord for real-time response.
Local Qwen Automation + RAG
Migrated routine OpenClaw/Sentinel automation workloads off paid cloud models onto local Qwen, preserving escalation paths for complex work. The workstation runs a 27B fallback model plus Open WebUI/RAG for homelab documentation, runbooks, and upgrade planning.
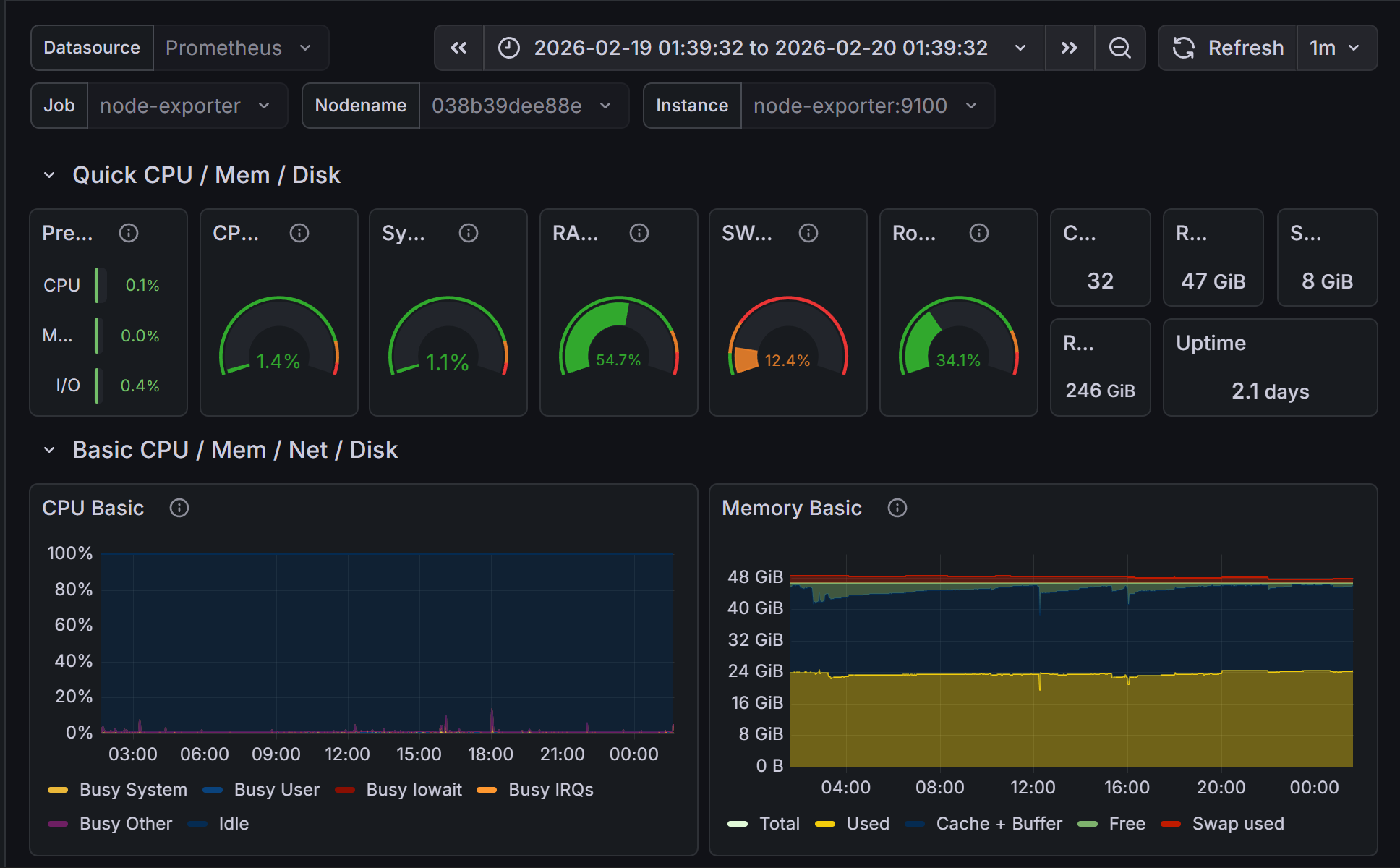
Prometheus + Grafana + Exportarr
Time-series monitoring with Prometheus scraping node-exporter (host metrics) and Exportarr (Sonarr/Radarr/Prowlarr). Grafana dashboards for resource utilization and service health.
Uptime Kuma
Service endpoint monitoring with HTTP/HTTPS checks, TCP port probes, DNS resolution tests, and alerting. Recovered from SQLite corruption and added a daily database integrity timer so monitoring fails visibly instead of silently rotting.
Git Config Backup
Private GitHub repo backing up all critical configs: Caddyfile, Wazuh rules/decoders, OPNsense config.xml, compose files, Cowrie plugins. Weekly automated push via cron.
Database Layer
PostgreSQL (Authentik, Wiki.js), MariaDB (media apps), Redis (caching), SQLite (N8N, Uptime Kuma). Each workload uses the appropriate data store.
Infrastructure
Two-node Proxmox VE lab with PCIe passthrough, SR-IOV networking, GPU acceleration, ordered boot sequencing, and backup coverage for critical workloads.
Proxmox VE - Two-Node Homelab
Intel i9-13900KF primary host plus M18 GPU node running QEMU/KVM VMs and LXC containers with UEFI boot, PCIe passthrough, SR-IOV networking, and deterministic startup ordering.
- Boot order: Cowrie → OPNsense → DNS → Cloudflared → CrowdSec (15s buffer) → Caddy → Docker → UniFi → Wazuh → Home Assistant → Uptime Kuma → Ansible → Unraid
- GPU services: Intel ARC A380 for media/transcoding plus NVIDIA GPUs for local AI model serving
- SR-IOV: 16 VFs on ConnectX-5, each assigned to a VM/LXC - no software bridge
- USB passthrough for Zigbee/Z-Wave controllers to Home Assistant
- All VMs/CTs set to
onboot: 1- full lab recovers unattended after power loss
Unraid NAS
Network-attached storage VM with parity-protected array. NFS/SMB exports mounted into Docker LXC for media and compute workloads. SATA controller passed through via PCIe.
Docker LXC - 40+ Containers
Privileged LXC with 16 cores, 24GB RAM, GPU passthrough, and Unraid NFS mounts. Runs ~40 containers including media, monitoring, SSO, threat intelligence, automation, and agent-support stacks.
NVIDIA BlueField-2 DPU
Staged LAN-offload upgrade plan for replacing the current ConnectX-5 LAN/workstation side with BlueField OVS/ASAP2 offload while keeping OPNsense on the existing WAN NIC. Includes day-of runbook, rollback plan, and RAG-ingested documentation pack.
Mellanox ConnectX-5
Dual-port 25GbE NIC with 16 SR-IOV Virtual Functions. Each VF assigned to a VM/LXC for line-rate networking without software bridge overhead.
Home Assistant + TinyHA Voice + Alexa
Smart home automation with a fully local AI voice pipeline: ESPHome ESP32-S3 satellites → M18 GPU Parakeet STT → TinyHA deterministic router → direct HA API actions, with Qwen 27B guarded fallback and a custom AWS Lambda skill for hybrid Alexa control.
Utilities
IT Tools, CyberChef, Stirling PDF, Wiki.js, Adminer, Notifiarr - operational tools for day-to-day administration and incident investigation.